What is Cyber Security?
Cyber security is a discipline that covers how to defend devices and services from electronic attacks by nefarious actors such as hackers, spammers, and cybercriminals. While some components of cyber security are designed to strike first, most of today's professionals focus more on determining the best way to defend all assets, from computers and smartphones to networks and databases, from attacks.
Cyber security has been used as a catch-all term in the media to describe the process of protection against every form of cybercrime, from identity theft to international digital weapons. These labels are valid, but they fail to capture the true nature of cyber security for those without a computer science degree or experience in the digital industry.
Cisco Systems, the tech conglomerate specializing in networking, the cloud, and security, defines cyber security as “…the practice of protecting systems, networks, and programs from digital attacks. These cyberattacks are usually aimed at accessing, changing, or destroying sensitive information; extorting money from users; or interrupting normal business processes.”
The Scale of the Cyber Security Threat
According to Forbes, 2022 will present us with a pack of diverse and terrifying cyber security challenges, everything from supply chain disruption to increased smart device risks to a continued cyber security talent drought.
According to Cybercrime Magazine, cybercrime will cost the world $10.5 trillion annually by 2025! Furthermore, global cybercrime costs are predicted to rise by almost 15 percent yearly over the next four years.
Concepts such as the pandemic, cryptocurrency, and the rise in remote working are coming together to create a target-rich environment for criminals to take advantage of.
How Does Cyber Security Work? The Challenges of Cyber Security
Cyber security encompasses technologies, processes, and methods to defend computer systems, data, and networks from attacks. To best answer the question “what is cyber security” and how cyber security works, we must divide it into a series of subdomains:
Application Security
Application security covers the implementation of different defenses in an organization’s software and services against a diverse range of threats. This sub-domain requires cyber security experts to write secure code, design secure application architectures, implement robust data input validation, and more, to minimize the chance of unauthorized access or modification of application resources.
Cloud Security
Cloud security relates to creating secure cloud architectures and applications for companies that use cloud service providers like Amazon Web Services, Google, Azure, Rackspace, etc.
Identity Management and Data Security
This subdomain covers activities, frameworks, and processes that enable authorization and authentication of legitimate individuals to an organization’s information systems. These measures involve implementing powerful information storage mechanisms that secure the data, whether in transition or residing on a server or computer. In addition, this sub-domain makes greater use of authentication protocols, whether two-factor or multi-factor.
Mobile Security
Mobile security is a big deal today as more people rely on mobile devices. This subdomain protects organizational and personal information stored on mobile devices like tablets, cell phones, and laptops from different threats like unauthorized access, device loss or theft, malware, viruses, etc. In addition, mobile security employs authentication and education to help amplify security.
Network Security
Network security covers hardware and software mechanisms that protect the network and infrastructure from disruptions, unauthorized access, and other abuses. Effective network security protects organizational assets against a wide range of threats from within or outside the organization.
Disaster Recovery and Business Continuity Planning
Not all threats are human-based. The DR BC subdomain covers processes, alerts, monitoring, and plans designed to help organizations prepare for keeping their business-critical systems running during and after any sort of incident (massive power outages, fires, natural disasters), and resuming and recovering lost operations and systems in the incident’s aftermath.
User Education
Knowledge is power, and staff awareness of cyber threats is valuable in the cyber security puzzle. Giving business staff training on the fundamentals of computer security is critical in raising awareness about industry best practices, organizational procedures and policies, monitoring, and reporting suspicious, malicious activities. This subdomain covers cyber security-related classes, programs, and certifications.
What is Cyber Security and Types of Cyber Threats
Cybercrime is defined as any unauthorized activity involving a computer, device, or network. There are three generally recognized classifications of cybercrime: computer-assisted crimes, crimes where the computer itself is a target, and crimes where the computer is incidental to the crime rather than directly related.
Here is a list of common cyber threats:
- Cyberterrorism. This threat is a politically-based attack on computers and information technology to cause harm and create widespread social disruption.
- Malware. This threat encompasses ransomware, spyware, viruses, and worms. It can install harmful software, block access to your computer resources, disrupt the system, or covertly transmit information from your data storage.
- Trojans. Like the legendary Trojan Horse of mythology, this attack tricks users into thinking they're opening a harmless file. Instead, once the trojan is in place, it attacks the system, typically establishing a backdoor that allows access to cybercriminals.
- Botnets. This especially hideous attack involves large-scale cyberattacks conducted by remotely controlled malware-infected devices. Think of it as a string of computers under the control of one coordinating cybercriminal. What’s worse, compromised computers become part of the botnet system.
- Adware. This threat is a form of malware. It's often called advertisement-supported software. The adware virus is a potentially unwanted program (PUP) installed without your permission and automatically generates unwanted online advertisements.
- SQL injection. A Structured Query Language attack inserts malicious code into a SQL-using server.
- Phishing. Hackers use false communications, especially e-mail, to fool the recipient into opening it and following instructions that typically ask for personal information. Some phishing attacks also install malware.
- Man-in-the-middle attack. MITM attacks involve hackers inserting themselves into a two-person online transaction. Once in, the hackers can filter and steal desired data. MITM attacks often happen on unsecured public Wi-Fi networks.
- Man-in-the-middle attack. MITM attacks involve hackers inserting themselves into a two-person online transaction. Once in, the hackers can filter and steal desired data. MITM attacks often happen on unsecure public Wi-Fi networks.
- Denial of Service. DoS is a cyber attack that floods a network or computer with an overwhelming amount of “handshake” processes, effectively overloading the system and making it incapable of responding to user requests.
As data breaches, hacking, and cybercrime reach new heights, companies increasingly rely on cyber security experts to identify potential threats and protect valuable data. So it makes sense that the cyber security market is expected to grow from $217 billion in 2021 to $345 billion by 2026, posting a Compound Annual Growth Rate (CAGR) of 9.7% from 2021 to 2026.
The Advantages of Cyber Security
Today's cyber security industry is primarily focused on protecting devices and systems from attackers. While the bits and bytes behind these efforts can be hard to visualize, it's much easier to consider the effects. Without cyber security professionals working tirelessly, many websites would be nearly impossible to enjoy due to ever-present denial-of-service attack attempts. Imagine not having access to Simplilearn's community of experts and certified professionals — no more tips, tricks, and advice to help you achieve your professional goals!
Without solid cyber security defenses, it would be easy to destroy modern-day essentials like the power grids and water treatment facilities that keep the world running smoothly.
Simply put, cyber security is critically important because it helps to preserve the lifestyles we have come to know and enjoy.
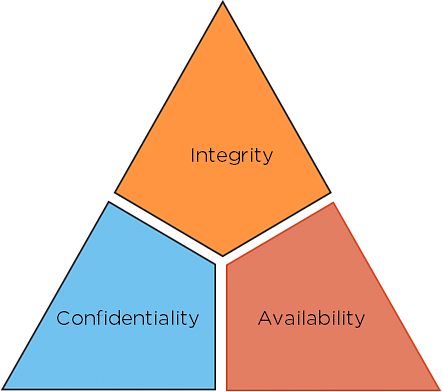
CIA Triad
The security of any organization starts with three principles: Confidentiality, Integrity, Availability. This is called as CIA, which has served as the industry standard for computer security since the time of first mainframes.
Fig: CIA triad
- Confidentiality: The principles of confidentiality assert that only authorized parties can access sensitive information and functions. Example: military secrets.
- Integrity: The principles of integrity assert that only authorized people and means can alter, add, or remove sensitive information and functions. Example: a user entering incorrect data into the database.
- Availability: The principles of availability assert that systems, functions, and data must be available on-demand according to agreed-upon parameters based on levels of service.
Who is a Cyber Security Expert?
As data breaches, hacking, and cybercrime reach new heights, companies are increasingly relying on Cyber Security experts to identify potential threats and protect valuable data. It makes sense that the Cyber Security market is expected to grow from $152 billion in 2018 to $248 billion by 2023.
So what do Cyber Security experts do? On any given day, they:
- Find, test, and repair weaknesses within a company's infrastructure.
- Monitor systems for malicious content
- Identify network breaches
- Install regular software updates, firewalls, and antivirus protection
- Strengthen areas where attacks may have occurred
They work in one or more of these common Cyber Security domains to keep data safe:
- Asset security: Analyze networks, computers, routers, and wireless access points
- Security architecture and engineering: Standardize security policies and procedures
- Communication and network security: Regulate cloud storage and data transfer
- Identity and access management: Track user authentication and accountability
- Security operations: Monitor security to identify attacks
- Security assessment and testing: Test security policies to ensure compliance with industry standards
- Software development security: Create and repeatedly test code
- Security and risk management: Identify potential risks and implement appropriate security controls
Cyber Security experts employ different tactics to secure computer systems and networks. Some of the best practices include:
- Using two-way authentication
- Securing passwords
- Installing regular updates
- Running antivirus software
- Using firewalls to disable unwanted services
- Avoiding phishing scams
- Employing cryptography, or encryption
- Securing domain name servers, or DNS